The Syrian Electronic Army has claimed another victim -- the Financial Times.
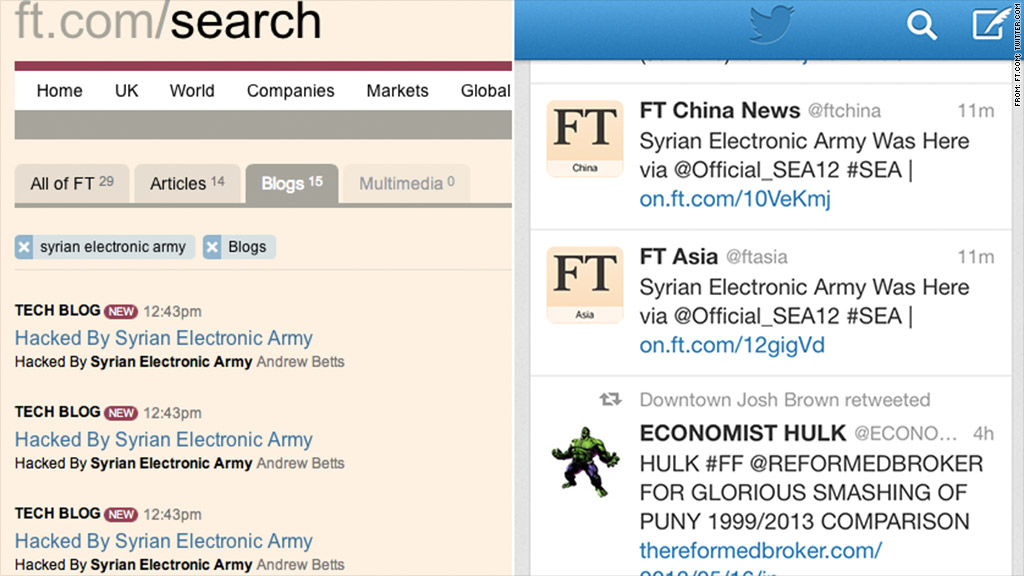
The pro-Syrian hacking group broke into one of the newspaper's blogs and some social media accounts, issuing tweets saying "Syrian Electronic Army Was Here" and blog posts proclaiming "Hacked by Syrian Electronic Army".
The attack comes just weeks after the same group hacked into the Associated Press Twitter account and issued a false tweet claiming that two explosions had hit the White House, injuring President Obama. That tweet led to a quick, sharp flash crash in U.S. markets.
A spokesperson for the Financial Times, part of the Pearson (PSO)publishing group, said it was working to clean up its accounts.
FT Adviser (@FTAdviser), which publishes news and analysis for investment professionals, tweeted: "Apologies for the random political ramblings folks - we were hacked. I suppose it's a compliment really."
Related: Is this your password? Change it.
In addition to the relatively harmless, graffiti-style posts, the hackers also issued tweets via FT accounts that linked to graphic, violent videos displaying what appear to be barbaric scenes from Syria's civil war.
The Syrian Electronic Army supports Syrian President Bashar al-Assad and has pursued a campaign of hacking against a wide range of accounts.
Over the past few months, the group claims to have hacked British broadcaster the BBC and U.S. outlets CBS News and NPR, as well as Columbia University and Human Rights Watch.
Related: Stop hackers in their tracks
Security pundits have called on Twitter for years to beef up its security using simple methods, such as limiting login attempts and allowing only one person to access an account at any time.
Many hope Twitter will eventually employ a "two-factor authentication" login method. It's a basic security tool already used by Google (GOOG), Facebook (FB) and Dropbox that requires both a password and a piece of data, such as numbers sent via text message.
Twitter began posting job listings earlier this year for engineers to work on two-factor authentication. The posts came after Twitter's own systems were hacked, and the attackers gained access to usernames and passwords for about 250,000 users.

