
Don't like getting hacked? Sorry, you'd better get used to it.
Every few weeks, we learn about another data breach. It's the privacy world's version of an oil spill. A hacker breaks into a company and grabs a database of our personal details. They're sold on the black market, and the exposure puts us at higher risk of fraud and identity theft.
Half of American adults were hacked this year. Floating out there somewhere is enough information to open bank accounts in your name and ruin your credit -- or get hunted down by an abusive ex-spouse.
Just this week, restaurant chain P.F. Chang's China Bistro lost a batch of customer debit and credit card data. Recently, hackers used malware to infect the payment terminals at Target, Michaels and Neiman Marcus. Cyberthieves wormed their way into the computer systems at Adobe, AOL, eBay and Snapchat. Criminals used a third-party company to nab credentials from Yahoo.
Never before in history has it been this easy to steal so much sensitive, useful information. But there's not a whole lot you can do about it. Here are four basic reasons these huge hacks will keep happening.
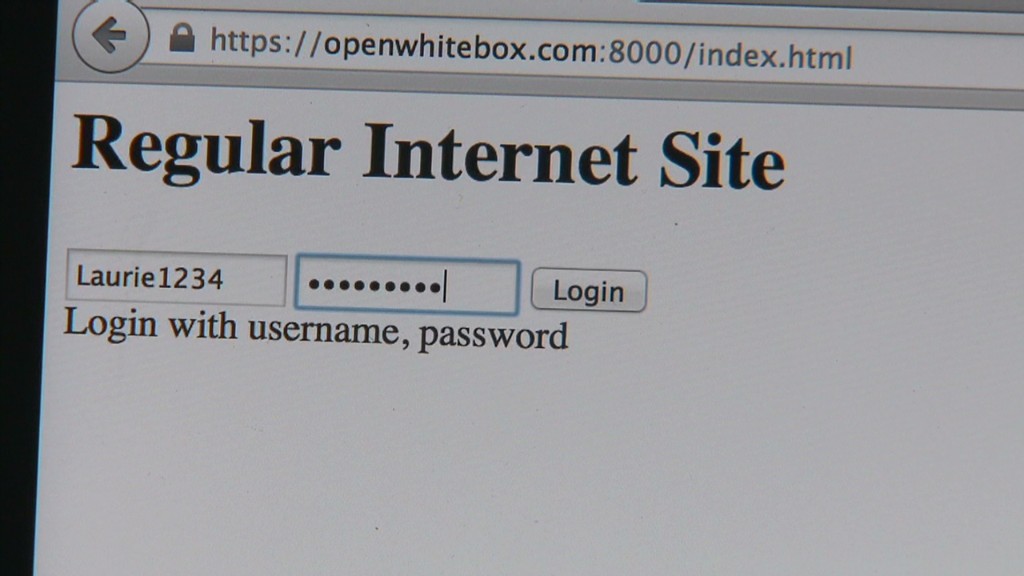
We've moved our lives online. Almost everything we do relies on devices hooked up to the Internet. When we interact with government services and customer support, the person on the other line is logging our details into computer servers. Retail stores use Internet-connected networks to process transactions.
Hewlett-Packard's (HPQ) most recent cybersecurity report noted how we're now more exposed than ever because we're tethered to mobile devices and weak Web software, including Flash and Java.
It's "an ever-expanding attack surface," said Jacob West, an executive at HP's division for business security products.
Expanded data collection. Retailers, hospitals, restaurants -- everyone is gobbling up our personal information and storing it behind our backs. Why did Target (TGT) keep the names, addresses, phone numbers and email for 70 million people?
Because that information has value. There's a thriving market for our personal details. Advertisers want more targeted commercials. Banks want to avoid bad lending. Data brokers and analytics firms supply them with profiles based on this information. It's just a giant treasure chest for hackers to loot.
Hackers are getting more tactical. Ditch the image of a lone, pierced-and-tattooed cyber punk. Modern day hacking operations are carried out by tech professionals gone rogue, oftentimes working in teams on behest of criminal organizations.
Meanwhile, hackers are doing their homework. They sneak into networks and lay quiet -- sometimes for years. Using that intelligence, hackers tailor malware specifically to attack a company's computers, said Brendan Hannigan, who leads the security systems division at IBM (IBM).
"One of the most significant things that's changed is the sophistication of the people doing damage," Hannigan said.
Those powerful offensive hacking weapons -- like the Zeus trojan software -- eventually show up for cheap on the black market. The way security experts see it, every two-bit hacker gets access to the cyber equivalent of a nuke.
Related: Simple tips to avoid getting hacked
Even boring data is now dangerous. Who cares if hackers get our names and birthdays? There's a mistaken belief this is easily discoverable, public information. It's not. But more importantly, these seemingly useless data points can now tie our whole lives together.
"The bad guys have figured out how to put together low-value data and turn it into something of value," said Patrick Peterson, CEO of email security firm Agari.
In essence, hackers are taking a lesson from legal data brokers. The same black market selling your stolen credit card is also selling your name and birthday. Armed with those three, criminals can more easily open accounts in your name.

