The Obamacare website has more than annoying bugs. A cybersecurity expert found a way to hack into users' accounts.
Until the Department of Health fixed the security hole last week, anyone could easily reset your Healthcare.gov password without your knowledge and potentially hijack your account.
The glitch was discovered last week by Ben Simo, a software tester in Arizona. Simo found that gaining access to people's accounts was frighteningly simple. You could have:
- guessed an existing user name, and the website would have confirmed it exists.
- claimed you forgot your password, and the site would have reset it.
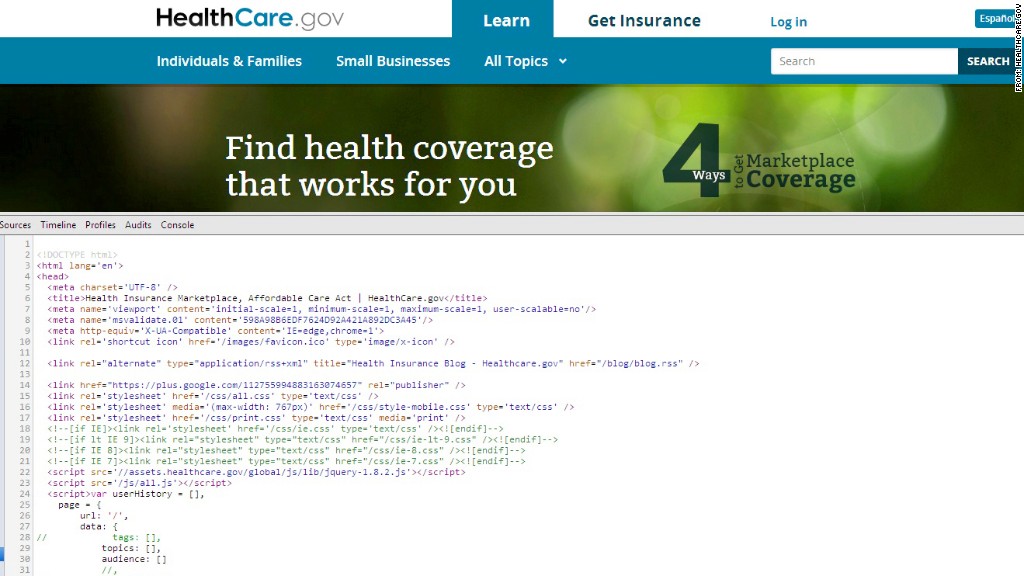
- viewed the site's unencrypted source code in any browser to find the password reset code.
- plugged in the user name and reset code, and the website would have displayed a person's three security questions (your oldest niece's first name, name of favorite pet, date of wedding anniversary, etc.).
- answered the security questions wrong, and the website would have spit out the account owner's email address -- again, unencrypted.
Armed with the account holder's email address, a person with malicious intent could easily track down their target on social media, where they'd likely discover the answers to those security questions.
It wouldn't have even taken a skilled hacker. Anyone with bad intentions -- and a minimal understanding of how to read a website's code -- could have figured it out. While such an attack might not have yielded your Social Security number or health information, it would have exposed your address and phone number.
Related story: Obamacare 'hub' back online after malfunction
By Friday, that dent in security was gone. But security consultants say it's disconcerting that such a privacy concern remained unaddressed for more than three weeks after the federal government launched the Obamacare website Oct. 1.
The Department of Health and Human Services, which is rolling out the health care overhaul, confirmed the flaws existed. After being contacted for this story, the department said changes were made that would prevent outsiders from seeing someone's password reset code.
"We have taken great care to ensure that people's usernames and information are kept secure," said health spokeswoman Joanne Peters.
Simo tried to report the defect as soon as he found it, but the Obamacare hotline operator referred him to law enforcement -- which was neither helpful nor relevant. While attempting to retrace Simo's steps on Friday, CNNMoney found that some of the issues had been fixed -- but not all.
Still, Simo fears that a savvy hacker could find other holes and Obamacare applicants' data will be compromised on a mass scale.
"This seems really sloppy," Simo said. "Either the developers were incompetent and did not know how to do the basic things to protect user information, or the development was so fractured that the individuals building the system didn't understand how they fit into the bigger picture."
Related story: Obamacare website: 6 biggest contractors
The flaw wasn't mentioned at last week's congressional hearing, when government contractors CGI Federal and Quality Software Services Inc. testified about their responsibilities in the project. But another point was made by Congressman Mike Rogers, R-Mich.: companies keep patching up the website's holes, and adding thousands of new lines of computer code, exposing the entire system to unforeseen security problems.
Cyberattacks on Obamacare exchange websites are already underway. At least one state, Connecticut, has seen outsiders attempt to gain "irregular" access, according to Jim Wadleigh, chief information officer of Access Health CT.
Congress' inquiries continued Tuesday, when the Ways and Means Committee posed questions about the site's glitches and security to Marilyn Tavenner, head of the health department's Centers for Medicare & Medicaid Services.
The security hole is just the latest in a series of mishaps for the Obamacare website's launch. In the first weeks, system errors prevented people from signing up to the newly launched insurance exchanges. Over the past weekend, a government contractor's network failure again left users unable to apply.
Monday brought the latest worrisome disclosure: that the entire Obamacare website operates on a single computer server in Virginia -- without any backup, according to Congressman Rogers.

