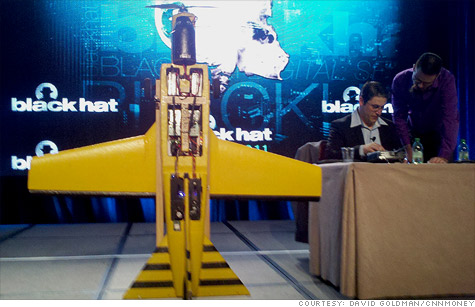
Security professionals Richard Perkins (right) and Mike Tassey built a tiny cyber plane that packs a big punch.
LAS VEGAS (CNNMoney) -- With a few thousand bucks, a tool box and some technical skill, you could bring about the cyber apocalypse.
Two security professionals proved as much at the Black Hat cybersecurity convention in Las Vegas on Wednesday. They showed off what they had been tinkering with for the past two years: a small, unmanned airplane that is capable of some truly remarkable -- and potentially disastrous -- hacks.
"If we can do it, they can do it," Richard Perkins and Mike Tassey repeated several times throughout their presentation.
Perkins is a security engineer supporting the U.S. government and Tassey is a security consultant for Wall Street firms. But after work, the long-time buddies would take off their cyber attack prevention hats, put on their evil hacker thinking caps, and build their airplane in Perkins' garage.
The plane can wreak lots of havoc.
For instance, it can fly over a Starbucks (SBUX, Fortune 500) and steal the personal information of everyone connected to the coffee shop's free Wi-Fi network. It can intercept your cell phone conversations and even reroute your calls to another number. It can trace the location of specific people and follow them home.
"There's a lot of evil stuff you can do from the sky," said Tassey.
Perkins and Tassey spent a total of just $6,190 to build the plane. They made a point to keep it relatively cheap and to buy components that were readily available to prove that literally anyone could make one.
"You don't need a Ph.D. from MIT to do this," said Perkins. "There are no custom parts, it was fabricated using hand tools, and very little coding is required. All you need is dedicated people."
With all the talk of how common it is for hackers to attack corporations and government agencies from remote locations from around the world, why would cyber attackers want a plane?
Cyber security professionals are furiously working to prevent attacks on their networks. Physical security staff are doing all they can to prevent the wrong people from walking into buildings in which they don't belong.
But Tassey said very few people are thinking about what information could be gathered from above.
That's troubling. An aerial cyber attack could be carried out without ever breaking through a firewall. Here's a hypothetical example.
An important executive or agency director could make a call on his or her cell phone when a cyber plane is overhead. The plane is capable of spoofing a cell tower and tracing a particular phone's signal. So it could follow a person home and steal information from a target's home network, which is less likely to be behind a strict firewall.
But the plane could also break into firewall-protected systems too.
The plane doesn't have much on board. To keep it light enough to fly, the plane sends signals back to a base station, which relays commands to and from a computer.
That PC can be controlled remotely over the Internet, meaning a group of attackers in diverse regions of the world can all work together to propagate an aerial cyber attack.
Fortunately, Tassey and Perkins said their plane could be used for good as well.
Law enforcement could use it in search and rescue operations to search for the cell phone signal of someone who is missing. In a disaster situation, the plane could be used to transmit Internet and cell phone signals to relief workers.
But when asked how to defend against an attack from a cyber plane, Tassey and Perkins said they didn't know if one could be prevented as of yet.
"It allows bad guys to have distance and anonymity," Tassey said.
In the cybersecurity battle, those are two things that have given malicious attackers a leg up. ![]()