If your PC is riddled with infections, they probably came in through files you installed yourself.
NEW YORK (CNNMoney) -- If your computer is infected, it's probably because of something you did, according to a Microsoft study released this week.
In its semi-annual Security Intelligence Report, the software giant found that the largest group of malware attacks on its Windows operating systems -- 44.8% -- occurred because of some kind of action taken by the computer's operator. It may have been as simple as clicking a link or downloading an infected file, but a human was the culprit.
But let's not be too hard on ourselves -- we were most likely duped into doing it. According to Microsoft's (MSFT, Fortune 500) report, one of malicious software's primary entry mechanisms is through phishing schemes.
Phishing schemes come in many forms. Often they are spam e-mails sent to thousands and sometimes millions of recipients, typically with the intention of getting the user to click on and open an infected file. They can be very rudimentary or incredibly sophisticated, depending on the skill of the attacker.
They're also hard to escape: Most of the e-mail messages sent over the Internet are unwanted, Microsoft said. It can also be difficult to discern phishing scams from wanted e-mails. Overall, 47.8% of phishing attacks sent in the first half of this year posed as legitimate e-mails from social networks like Facebook, according to the report. Banks and other financial institutions were also popular camouflage for bait e-mails.
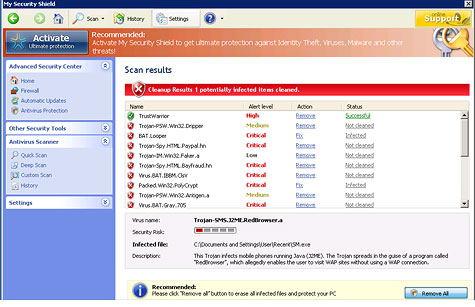
When malware, or malicious code, is installed as a result of a clicked-on link or downloaded file, it can give hackers any number of capabilities, including complete control of an infected computer. If a computer infected with malware is connected to a network, attackers can often access other connected systems and servers.
Since humans are behind such a large chunk of computer infections, Microsoft suggested that security professionals rethink the way they approach security.
"IT professionals are accustomed to thinking about the technical aspects of security; however, as this report has shown, the human element has become just as important for attackers as the technical element, if not more so," the report's authors wrote.
"By implementing effective technical safeguards, programs, and processes designed to defend against social engineering, you can help your users avoid being taken advantage of by attackers," they continued.
Of course, the technical side of security remains important. Microsoft reported that 43.2% of PC attacks were automatically installed by taking advantage of Microsoft Windows' AutoRun function in the XP and Vista versions of the operating system, which automatically executes certain files and programs. As a result, Microsoft in February released an update to make the AutoRun feature more secure. Windows 7 already had the more secure AutoRun feature set up as its default option.
About 6% of attacks on Windows PCs were attributed to other kinds of exploits -- malicious codes that attempt to take advantage of known vulnerabilities in applications or operating systems.
Exploits of Oracle's (ORCL, Fortune 500) Java software, which runs rich applications on the Web, was responsible for between 33% and 50% of all exploits during each of the past four quarters, Microsoft said. Nearly all document exploits this year targeted Adobe (ADBE) Acrobat and Reader.
Despite alarm bells and widespread coverage in the media, only about 0.1% of successful attacks were from so-called "zero-day" exploits. Zero-day exploits are attacks on a newly discovered security problem in an application or software, which the vendor had not had time to patch before the attack.
Those attacks, while extremely rare, capture a lot of attention because they're theoretically impossible to defend against, leaving consumers and security professionals at the mercy of attackers.
Though zero-day exploits "continue to capture the imagination," Microsoft found that those fears are mostly misplaced. The vast majority of zero-day vulnerabilities are immediately patched once discovered and are never exploited.
Newer protections baked into the Windows operating system can also help mitigate attacks.
The newer the version of Windows you have, the less likely it is to get infected. About 1% of computers running Windows XP were found to have infections, according to Microsoft. That dropped off to roughly 0.5% with the latest Windows Vista software and just 0.15% of machines running the latest Windows 7 version. ![]()