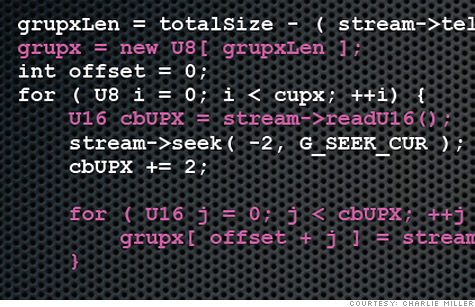
This code snippet is part of a bug that let security researcher Charlie Miller take control of an N9 phone.
LAS VEGAS (CNNMoney) -- Don't let Charlie Miller stand too close to you. The former NSA analyst turned freelance hacker could be trying to seize control of your phone.
Miller set the Black Hat cybersecurity conference buzzing on Wednesday with a presentation showing off newly discovered vulnerabilities in "near field communications" features on Samsung and Nokia devices. NFC is a short-range wireless technology that's coming soon to all major smartphones. It's intended to let you beam content to nearby devices and use your phone as a mobile wallet, but it could also be a flashing neon target for hackers.
Miller's most startling demo involved completely taking over an Android phone by merely brushing a tag with an embedded NFC chip against it.
A built-in content sharing feature called Android Beam allowed the tag to push a webpage to the Samsung Galaxy Nexus. A browser bug then opened the gate for unlimited access to everything on the phone.
Miller found similar vulnerabilities in the second phone he tested, a Nokia N9 running MeeGo. If the default "content sharing" setting is enabled, an attacker can work a loophole to pair the phone with a second device and go nuts.
The scenarios Miller showed off are spooky, but they're also far-fetched -- something even he admits. The Android attack exploited a bug that Google has already patched. Nokia's N9 sold poorly and runs an operating system that is being phased out.
"There's like three people in the world I could totally own with this," Miller quipped while showing off his N9 hack.
But Miller's stunt is an early alarm about a technology that will soon be ubiquitous. Google (GOOG, Fortune 500), Apple (AAPL, Fortune 500), Visa (V, Fortune 500), MasterCard (MA, Fortune 500) and other power players are eying NFC as the key to mobile wallet technology -- the "pay with your smartphone" option that's now trickling out to early adopters.
Miller picked the N9 and Nexus for his experiments, which began nine months ago, because they were the only major phones available with built-in NFC technology at the time. The real explosion will come in the next year. Apple is rumored to be including NFC in its next iPhone, and Google, which made NFC the basis of its Google Wallet technology, is pushing it hard on Android devices.
The big challenge for would-be NFC hackers is proximity. NFC signals have a tiny range that typically covers just a few centimeters. An attacker has to get very, very cozy with you and your devices to successfully transmit anything malicious. On Android phones, the content beam only works when the device is turned on and unlocked.
That's one reason the vendors aren't yet especially worried about NFC-based attacks.
"Nokia is not aware of any malicious incidents on the Nokia N9 due to the alleged vulnerabilities," Nokia (NOK) said in a written statement responding to Miller's presentation.
The company added that it's "unlikely that such attacks would occur on a broad scale," but said it is investigating the vulnerabilities that Miller publicized. Google declined to comment on the issue.
Miller can envision a few lines of attack. In Europe, for example, some movie posters include NFC chips that launch video trailers. Slip a malicious tag behind one of those posters and you can mess with fans' phones, sending them ads and other unwanted spam. Or stick an NFC tag on a checkout terminal and start transmitting data to the devices customers willingly swipe past.
Those 3-D "QR" barcodes have long had similar vulnerabilities.
Miller's tag exploit was actually an almost accidental discovery. He spent months building and refining a jury-rigged system for "fuzzing" NFC systems, a hacker technique that involves throwing vast amounts of random data at a piece of software in the hopes of crashing it.
Several months of almost round-the-clock fuzzing yielded a pretty minor bug collection. That's an indication that NFC implementation code is actually pretty good so far -- Miller said he was surprised he didn't find more flaws.
The tag loophole, though, allowed much more manipulation than he expected. Miller would like to see phone makers rethink their frictionless-sharing approach. Devices should at least ask permission before accepting data from unfamiliar devices or NFC tags that just happen to be nearby, he thinks.
NFC is still essentially experimental, and like any cutting-edge technology, it has some unanticipated consequences.
"Hopefully my talk was more of a sort of warning of what could happen, rather than 'Android bad,'" Miller said. ![]()